Emma O'ConnorMicrosoft's 2023 Digital Defence Report: Key Insights
The critical shift from detecting breaches to proactively preventing them.
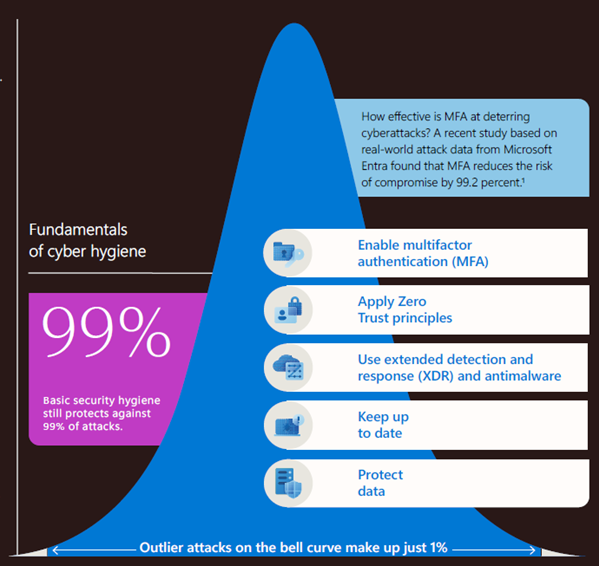
The 2023 Microsoft Digital Defence Report is a pivotal shift from detecting breaches to proactively preventing them. It emphasises Cyber Resilience and unveils five critical measures preventing 99% of attacks:
- Multi-Factor Authentication (MFA) across all user accounts
- Zero Trust: Verify users and devices before granting access
- XDR & Antimalware for extended detection and response
- Regular Updates to patch vulnerabilities
- Protecting Data: Identifying sensitive data and controlling access
*Copyright the Microsoft Digital Defence Report 2023.
Rising Ransomware Threats: The Unmanaged Device Risk
Unmanaged devices contribute to 80-90% of successful attacks, a significant concern highlighted in the report. As ransomware evolves, attackers exploit personal and BYOD devices. It's crucial to discover and protect all devices accessing corporate data, including unmanaged devices.
Ransomware Evolution: Tactics and Defence Strategies
Attacks involve data exfiltration in 13% of cases, necessitating a ransom payment. Attack vectors include exploiting external services, vulnerable applications, and unauthorised user access. Attackers now target less common applications, demanding a comprehensive view of software vulnerabilities.
Utilising Legitimate Remote Monitoring and Management Tools
Attackers are now using Remote Monitoring and Management tools to deploy ransomware undetected. Application control policies and a consolidated global software inventory defend against these attacks.
Microsoft’s Ransomware Task Force
The task force aims to disrupt ransomware business models, mapping payment ecosystems. Key insights recommend AI-powered EDR, migrating to the Cloud, integrating cybersecurity as an organisational risk, and collaborative security tools.
Optimal Ransomware Resiliency State
Microsoft advocates a proactive defence approach against ransomware, outlining five foundational measures. These include:
- Modern authentication
- Least privileged access
- Threat-free environments
- Posture management
- Automatic cloud backups
The Persistent Phishing Menace
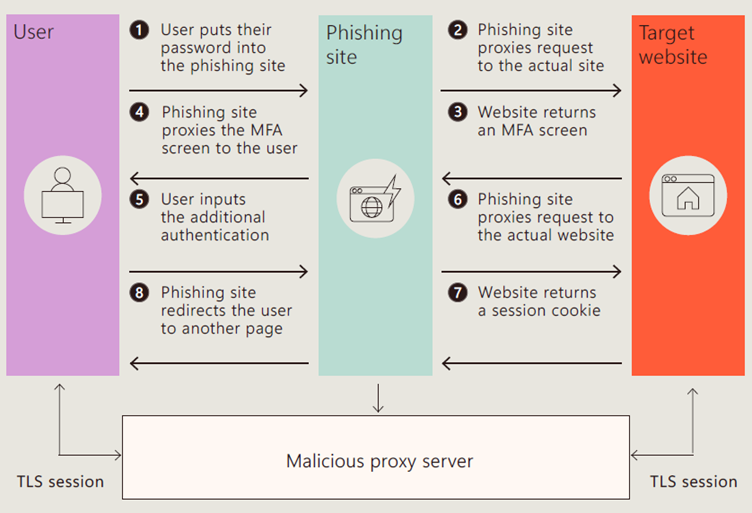
Phishing attacks, especially Adversary-in-the-middle (AiTM) tactics, continue to increase in sophistication. Identity attacks on Microsoft Entra have skyrocketed, emphasising the critical need for MFA on all user accounts.
Best Practice Security Measures
Implement strong password practices, offline synced password safes, and always use MFA, especially for VPN and Email accounts.
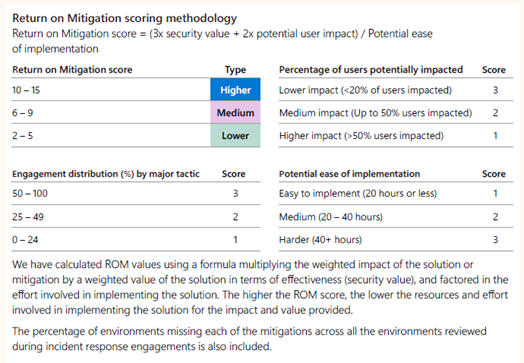
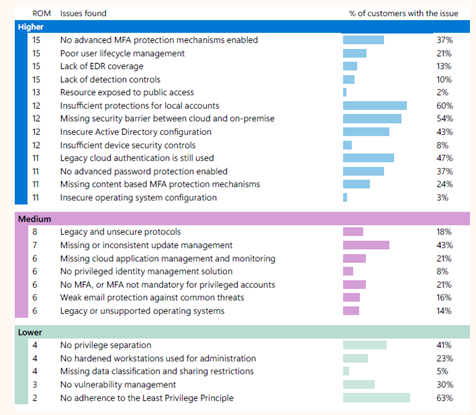
Return on Mitigation: Targeting Investment for Resilience
Microsoft highlights a methodology to calculate security measure effectiveness, emphasising the top cybersecurity recommendations for maximum mitigation.
In summary
The 2023 Microsoft Digital Defence Report emphasises the critical shift from detecting breaches to proactively preventing them. It underscores the importance of fundamental cybersecurity measures, a concept that aligns perfectly with ThreatAware's founding principles.
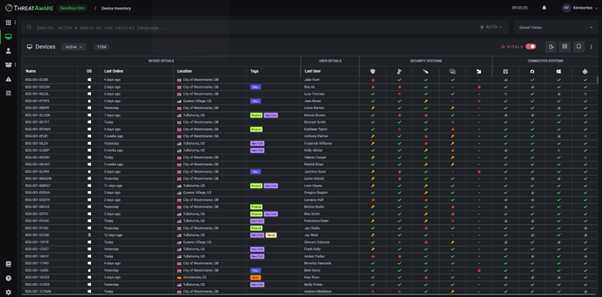
In a landscape witnessing a surge in cyber-attacks despite the abundance of security tools, ThreatAware recognises the necessity for comprehensive security grounded in a clear understanding of all IT assets. The report echoes this sentiment, highlighting the need for a better approach amidst the challenges posed by hybrid work setups and evolving cloud systems.
ThreatAware's vision is anchored in unified data for comprehensive visibility, emphasising fundamental protections as a primary defence against the majority of cyber threats. The emphasis on simplicity aligns with the report's findings, suggesting that a streamlined approach can drive effective action in cybersecurity.
The synergy between ThreatAware's vision and the insights from the Microsoft report emphasises the critical need for a proactive and comprehensive cybersecurity strategy, one that not only encompasses fundamental measures but also aligns with the evolving nature of IT landscapes.
With ThreatAware, these best practices become a reality, safeguarding all cyber assets against an ever-evolving threat landscape.
Secure Every Device in Your Network
Instantly uncover and protect every asset in your IT estate with ThreatAware.
Identify unknown devices, reconcile asset data across platforms, and eliminate security gaps to ensure continuous cyber hygiene.
Request a Trial