Beyond Cyber
Use Cases
ThreatAware delivers benefits that extend beyond the cybersecurity team, empowering company boards to better understand and manage cyber risks, while enabling procurement teams to streamline device lifecycle management.
IT Asset Management
Discover how ThreatAware's API discovery, time-matching, and dynamic configuration elevate asset management to the next level.

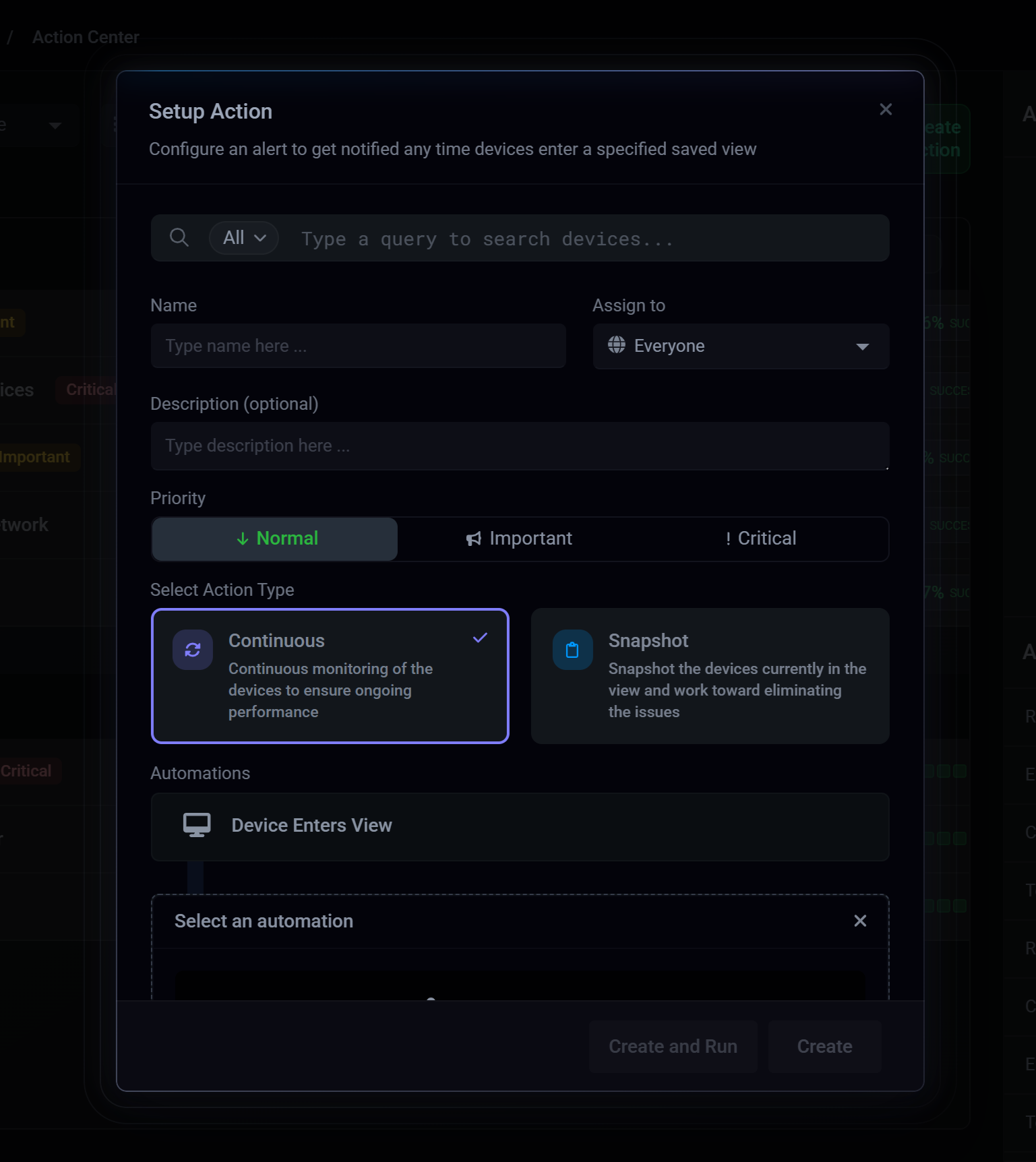
Cyber Hygiene
Find out how ThreatAware can help you efficiently and continuously monitor the status of your estate's controls.
Cyber Asset Attack Surface Management
Explore how ThreatAware can highlight gaps in your attack surface and help you reduce them.

Cyber Risk Reporting
Learn how ThreatAware can support you in generating accurate, user-friendly cyber risk reports to help drive change and mitigate risks.
ThreatAware has transformed the way leading organisations secure their cyber assets worldwide
"The cyber posture of the business doesn't stand still and ThreatAware is a single source of truth. Being made aware of devices that don't have the requisite software installed and functioning as expected is vital from a security perspective."
Lyndon Arnold, Head of IT, BGF