Cyber Risk Reporting
ThreatAware delivers actionable cyber risk insights, offering both granular and broad visualisations of your organisation's assets. It overcomes the limitations of standalone tools and manual processes, providing an accurate, holistic view to ensure compliance. This enables Boards to effectively track and manage regulatory requirements. In a typical deployment, we identify 20% of controls that are functioning but not correctly configured - creating hidden risks in your security posture.





Key Benefits
Streamline Compliance and Cybersecurity Management
Simplify audits, automate asset tracking, and centralise your tools with a unified, data-driven dashboard.
"You can't be 100% certain that your security controls are deployed and correctly functioning throughout your estate when relying on disparate tools. You need a single source of truth that correlates results from multiple systems and corroborates evidence. That's just a reality of modern computer systems."
- Seamless Audit Compliance Guarantee a smooth audit process by showcasing strong, effective cybersecurity management.
- Automated Asset Discovery Reduce manual tasks with real-time asset tracking and validation, making compliance reporting effortless.
- Unified Dashboard Streamline your workflow by merging multiple tools into one dynamic, data-driven dashboard, offering complete visibility into vulnerabilities and risks.
Key Features
Take Control with Actionable Insights
Transform insights into action, customise dashboards, and ensure continuous protection with automated updates and security validation.
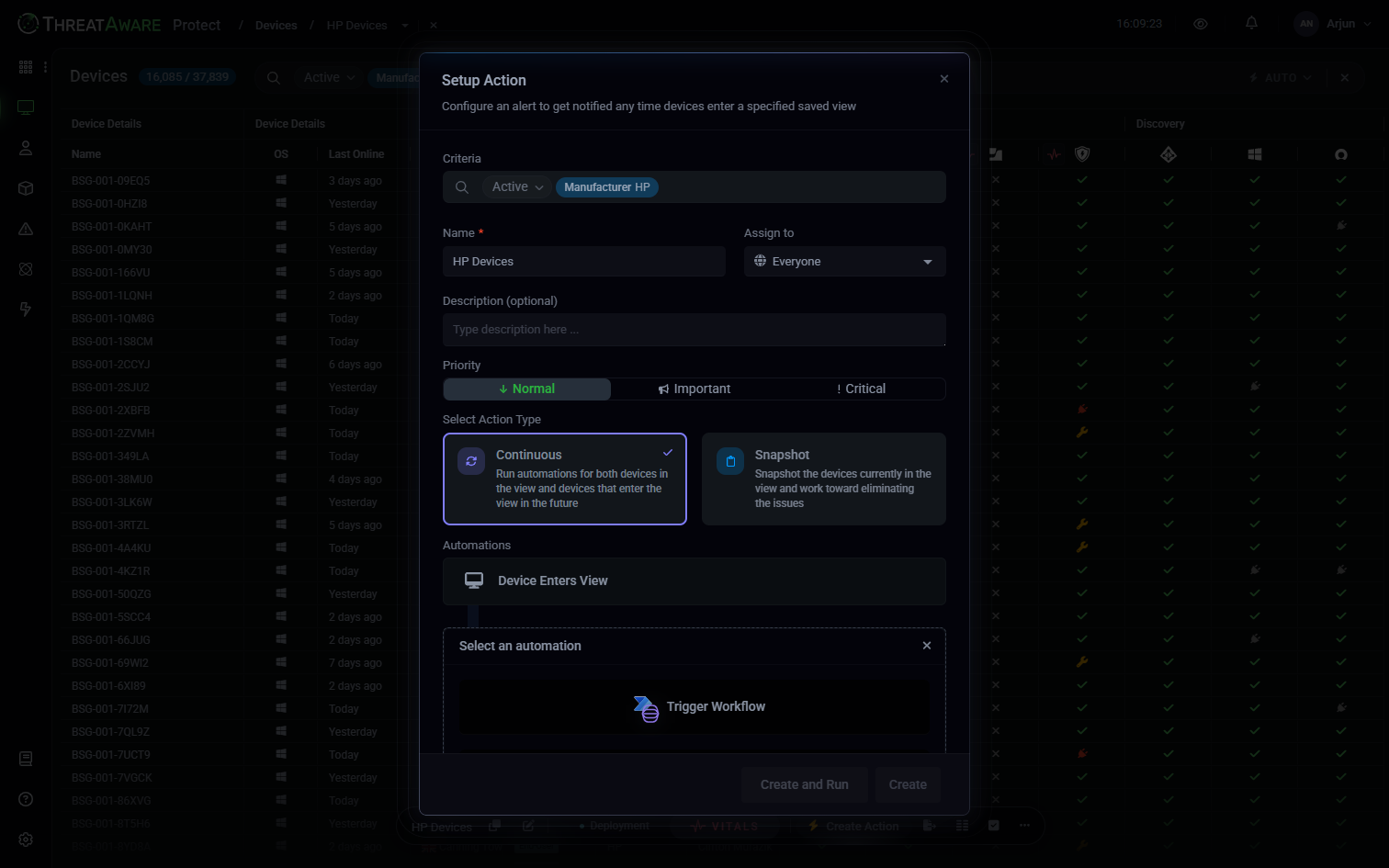
- Actionable Remediation Turn visual insights into prioritised actions with automated workflows that alert your team to vulnerable devices, enabling quick, effective remediation.
- Custom Dashboards Build personalised dashboards using ThreatAware's comprehensive data, allowing precise reporting and analysis tailored to your needs.
- Automatic Updates Ensure accurate, up-to-date visibility of your cyber assets with continuous automatic updates.
- Security Validation Regularly verify the deployment and functionality of security tools across all devices, minimising the risk of security gaps during transitions.
ThreatAware has transformed the way leading organisations secure their cyber assets worldwide
"The cyber posture of the business doesn't stand still and ThreatAware is a single source of truth. Being made aware of devices that don't have the requisite software installed and functioning as expected is vital from a security perspective."
Lyndon Arnold, Head of IT, BGF